Human interactions, public services, and economic exchanges are increasingly moving into the digital sphere, creating a growing need for identification, authentication, and authorisation, three essential functions of digital identity in economic and civic relationships.
In this context, where digital sovereignty, cross-border collaboration, and the integration of new technologies such as AI and blockchain are becoming strategic, digital identity is emerging as a central pillar of the digital infrastructures of tomorrow.
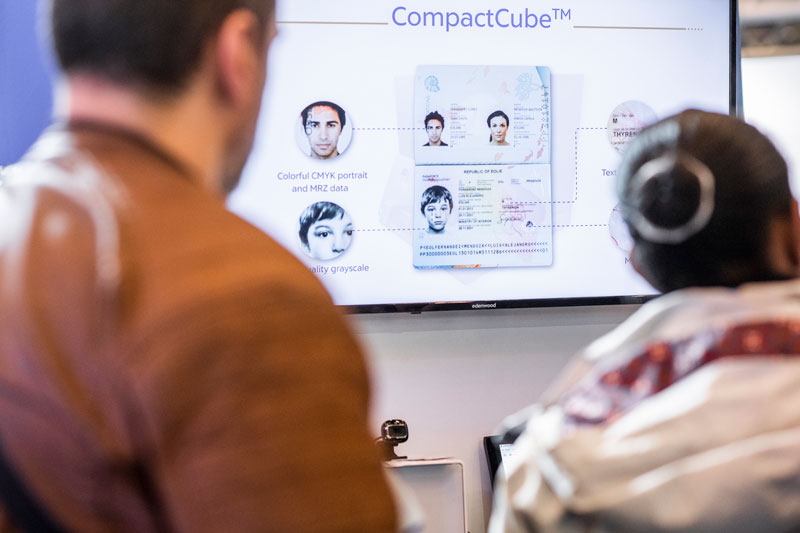
Discover the identification technologies, one of the major themes addressed by the TRUSTECH Event.
Digital Identity more Important than Ever!
In response to these new needs, the development of these functions continues to grow at a rapid pace. Identification has evolved to be able to verify information remotely, control the real presence of the person to be identified, and ensure the correct assignment of the documents and data presented. Biometrics and artificial intelligence, along with the orchestration of data source verification, have become essential in the identity verification process. These technologies, when governed responsibly, enhance reliability without compromising privacy, a key challenge in building human-centred digital governance.
Authentication has been considerably strengthened. Under both regulatory pressure and the need to manage risk and fraud, multi-factor authentication (MFA) has become a standard. Online accounts, payment services, transactions: almost all market players have adopted new practices, with numerous technological innovations emerging in the process. Authentication is also undergoing a major transformation, with the rise and generalisation of passwordless methods that use cryptographic protocols and biometric devices to enhance security without compromising user experience. Indeed, the use of biometrics, such as facial recognition and fingerprints, is becoming more widespread to reinforce the security of digital identities. Post-quantum cryptography is starting to be explored to prepare identity systems for future threats, while ensuring their sustainability in an increasingly complex digital ecosystem.
Authorisation, a crucial step despite its various components (digital signature, access management, resource allocation), takes into account the trust levels of identification, authentication, and network security. It has also diversified thanks to more advanced contextual and dynamic risk analysis, as well as customer behaviour and new tools for remote analysis and interaction. In connection with new cloud service platforms and connected devices, these essential identity functions use, combine, and transform multiple forms of certified data, such as physical and/or digital documents, identity attributes, or application tokens.
Governments Facing the Challenges and Opportunities of Digital Sovereignty
At the national level, choices regarding digital infrastructures and architectures have become more urgent given the new situation. The Zero Trust architecture has been implemented by businesses wishing to adopt these models. It requires strict identity verification for every access and resource in order to protect systems from internal and external threats. Governments and states are now confronted with the need to build not just simple e-service platforms, but genuine digital ecosystems capable of meeting the needs of the population in a resilient manner, including for key services in administration, education, healthcare, inclusion, and assistance. This includes the ability to integrate interoperable modules, standardised digital components, and decentralised technologies that promote transparency, resilience, and citizen trust.
The designed ecosystems must meet increasing requirements in terms of security, data protection, and technological sovereignty. Building these ecosystems is both a challenge and an opportunity to shape the national and/or regional digital landscape. The infrastructures must also be able to adapt to the rapid evolution of digital economic models linked to blockchain and crypto-assets, while ensuring robust governance. A crucial point is the respective role of the public and private sectors. Both sectors need each other to build a trusted ecosystem that is economically viable and operates in a sovereign manner.
As part of this challenge, states must also strengthen their governance over digital ecosystems. Beyond legal aspects relating to cybersecurity, identity management, and data protection, organising governance between the public and private sectors is important, and the establishment of an independent supervisory authority capable of encouraging and overseeing the various ecosystem actors is considered good practice. For their part, users are becoming more aware and responsible regarding the importance of protecting their digital identity.
The effort and investment in infrastructure may seem significant, but they are the price governments must pay if they want to retain their ability to act in digital intermediation, which concerns both economic flows and civic and social relations.
The Mobile Digital Wallet: a Revolution?
For several years, a revolution has agitated the digital sector: the mobile digital wallet, the famous “e-wallet”. For some time, the smartphone has served as a platform for certified documents or attributes presented in the form of two-dimensional codes (such as QR codes) or within applications. Digital identity is now taking the lead in a multitude of attestations and attributes for civil registry, administration, KYC (Know Your Customer), payment, diplomas, and more.
How can public and private data be orchestrated and certified while respecting data security and user consent? This is the challenge being addressed by a multitude of public and private initiatives.
These efforts must consider requirements for international interoperability, technological modularity, and open standards to ensure smooth cross-border collaboration. With the entry into force of the eIDAS 2.0 regulation, Europe plans to launch digital identity wallets, transforming authentication methods and facilitating secure access to online services. This EUDIW (European Digital Identity Wallet) project proposed by the European Commission is a major step forward in digital identity. At this stage, only one certainty remains: the digital wallet will fundamentally change how we experience digital identity.
For example, with more integrated journeys (including all steps of identification, authentication, and authorisation) and above all a smoother experience for users. This shift is part of a broader transformation of digital public services, where trust, a seamless experience, and control over personal data are priorities. The use of mobile phones as multi-purpose supports represents a major opportunity for the development of digital identity but is also reshaping market perspectives.
Renewed Perspectives
Solutions are needed to address challenges related to security, privacy, and sovereignty in the context of mobile operating systems and the overall cloud-mobile technology environment. The card is also gaining increased importance as a reliable and distinct identification and authentication factor, for use in combination with or as a complement to a smartphone.
Centralised, federated, and decentralised architecture models are also evolving towards complementarity. The rise of Web3 and “web of trust” approaches is redefining the way users control and share their identities across multiple digital environments. The paths of digital identity are expanding with the multiplication of use cases, while technologies and architecture models diversify. With these perspectives, the pursuit of greater international interoperability is also becoming increasingly prominent. Intense collaborative work is underway to enable the opening of protocols and the maturation of market standards. This work is essential to support the rise of cross-border public services, governed by appropriate, resilient, and inclusive governance.
This brief overview of identification and its developments highlights its growing importance for governments and citizens as well as all economic actors.
TRUSTECH is an opportunity to reconnect with major public and private stakeholders on the subject of digital identity and its technologies.
The key topics covered in this article—new identification and authentication practices, government initiatives, mobile digital wallets, new perspectives—will be discussed and explored through several conferences, with contributions from institutional representatives and experts. Technological solutions from the most innovative and renowned partners in the sector and numerous demonstrations will be available throughout the three-day event.

